If you are looking for a great way to engage your key stakeholders and identify project risks, perform a SWOT Analysis. Project managers or other facilitators can use this powerful tool to identify strengths and weaknesses. Furthermore, strengths may give rise to opportunities and weaknesses may lead to threats. Let's look at how to perform a SWOT Analysis.
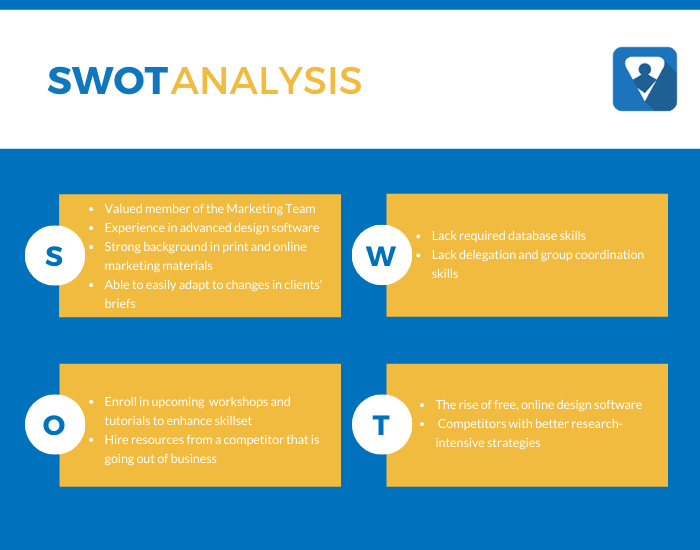
SWOT Example
What is SWOT?
Strengths. Something that an entity, department, or team is good at doing or that gives it a critical capability. A strength may be a skill, expertise, valuable resource, a competitive capability, or an attribute that provides a competitive advantage.
Weaknesses. Something an entity, department, or team lacks or does poorly or a condition that puts it at a disadvantage.
Opportunity. Upside risks that may cause positive effects to our project objectives. An example would be to exploit a discount savings by purchasing in bulk quantities.
Threats. These downside risks may cause negative effects to our project objectives. What are your obstacles? What may hinder your ability to achieve your project objectives?
More...
Tip:
The SWOT Analysis may be used at different levels of an organization including enterprise, departments, teams, and projects to name a few.
The SWOT Analysis is often used for enterprise and company strategic planning. In a classic sense, the Strengths and Weaknesses are viewed as internal and Opportunities and Threats as external factors (e.g., regulations, competitors, markets).
Alternatively, project risks—threats and opportunities—are uncertain events or conditions that, if it occurs, has a positive or negative effect on one or more project objectives. In the orientation of the SWOT Analysis, define these terms and provide examples. Furthermore, clarify the scope of the analysis.
Who Should Be Involved?
Invite key stakeholders to the SWOT Analysis meeting. These subject matter experts should have a strong knowledge of the topic. For example, perform a SWOT Analysis for the Accounts Payable systems and processes. Or perhaps you wish to evaluate the company's customer support team and processes.

Key Stakeholders
How to Conduct a SWOT Analysis
Brainstorm
Start with Strengths. Ask the meeting participants to write down the strengths. Then start a round-robin by asking the first person for one strength. Capture the strength on a white marker board or Cling Sheet with a unique identifier (e.g., 1.). Ask the next person for a strength and capture it (e.g., 2.). Continue the process until you've captured all of the ideas. If an individual runs out of ideas, they may pass.
Why have participants write the strengths first? This practice avoids groupthink, where a powerful, influential person speaks first and everyone follows. We want each person's voice to be heard equally.
Tip
Some people prefer the TOWS Analysis where you start by identifying and analyzing the Threats and Opportunities first. Then follow with the Weaknesses and Strengths.
Analyze and Combine
Once you have captured all of the strengths, combine common strengths if they are similar.
Prioritize
Number the greatest strength at the top of your list with the #1 (I use a different color marker). Then number the next greatest strength #2. Continue until all strengths are numbered in descending order.
Perform Steps 1-3 for Weaknesses, Opportunities, and Threats
Once you have identified, analyzed, and prioritized the strengths, perform steps 1-3 for Weaknesses, Opportunities, and Threats.
Identify Risks
Next, we identify risks. What are the threats and opportunities that may impact our project objectives significantly? Write and capture your risk statements in your risk register.
Define Risk Response Plans
Here's where the SWOT Analysis is so powerful. Analyze and combine your strengths, weaknesses, opportunities, and threats to create strategies. Define how you will get from where you are to where you want to be.
For example, we can use strengths to overcome weaknesses or to mitigate threats. Or we might exploit an opportunity to reduce a threat. Capture your risk response plans in your risk register.
7 Ways to Identify Project Risks
There are numerous ways to identify risks other than a SWOT Analysis. Project managers may want to use a combination of these techniques:
- Interviews
- Brainstorming
- Checklists
- Assumption Analysis
- Cause and Effect Diagrams
- Nominal Group Technique (NGT)
- Affinity Diagram
